Why this matters now
Clinical care and digital systems are now inseparable: downtime, data loss, or degraded information integrity can translate directly into delayed treatment, diagnostic uncertainty, and patient harm. Strengthening AI in healthcare must therefore be treated as an operational priority — not a back-office checkbox — because cyber failures cascade into safety, compliance, and reputation risk.
Two concurrent trends sharpen the urgency. First, high-profile incident tallies from 2025 show a disproportionate concentration of ransomware activity against healthcare entities, indicating persistent adversary focus on clinical environments. Second, growing clinician concern about social platforms undermining public health understanding creates a parallel vulnerability: misinformation-driven behavior can complicate incident response and create fertile ground for targeted social-engineering campaigns.
Ransomware penetrating clinical continuity
The mechanics of ransomware attacks in hospitals are changing. Attackers increasingly seek not just data ransom but operational leverage: locking imaging archives, disrupting lab integrations, or compromising scheduling systems creates immediate clinical friction. These interruptions produce quantifiable downstream effects — postponed procedures, extended ED stays, and additional administrative burden for clinicians who must resort to manual workarounds.
Root causes are familiar yet persistent: aged medical devices with limited patchability, insufficient network segmentation between clinical and administrative environments, and infrequent, scenario-driven recovery drills. Tackling these requires investment in both technology (endpoint detection, immutable backups, segmentation) and governance: incident playbooks that designate clinical decision authority and prioritize patient-safety-preserving actions during containment and recovery.
Information operations and social platforms as a threat vector
Misinformation is usually discussed in public health terms, but it also alters the attack surface for cybercriminals. When a sizable share of patients adopt harmful health behaviors sourced from short-form social platforms, organizations face sudden, anomalous care demands and higher volumes of sensitive communications. Threat actors can exploit these conditions, combining disinformation with phishing and extortion narratives to amplify pressure on institutions during incidents.
Operational defenses therefore need to bridge cyber threat intelligence and communications monitoring. This means integrating public-facing misinformation tracking into incident response, aligning digital outreach with technical containment timelines, and training communications teams to operate within the incident command structure from day one.
Call Out: Monitor public discourse as part of cyber defense — misinformation can magnify operational strain and be weaponized in extortion or phishing campaigns. Rapid, coordinated communications reduce leverage and restore patient confidence.
Collaborative models: marketplaces and regional readiness
Partnerships that pool expertise and services are becoming a pragmatic route for under-resourced hospitals. Marketplaces and alliance-led programs offer standardized assessments, shared incident response retainers, and procurement channels for vetted security tools. These models lower the cost barrier to baseline hygiene — patch orchestration, identity controls, and centralized logging — while creating regional cohorts capable of coordinated responses.
However, centralized services have limits. They can standardize tooling and detection but cannot substitute local clinical knowledge needed for rapid continuity decisions. The most resilient approach stitches together shared technical capabilities with locally empowered incident commanders who can make patient-centered tradeoffs under stress. Contract clarity — who owns containment, who funds recovery, and how liabilities are allocated — is essential before a crisis occurs.
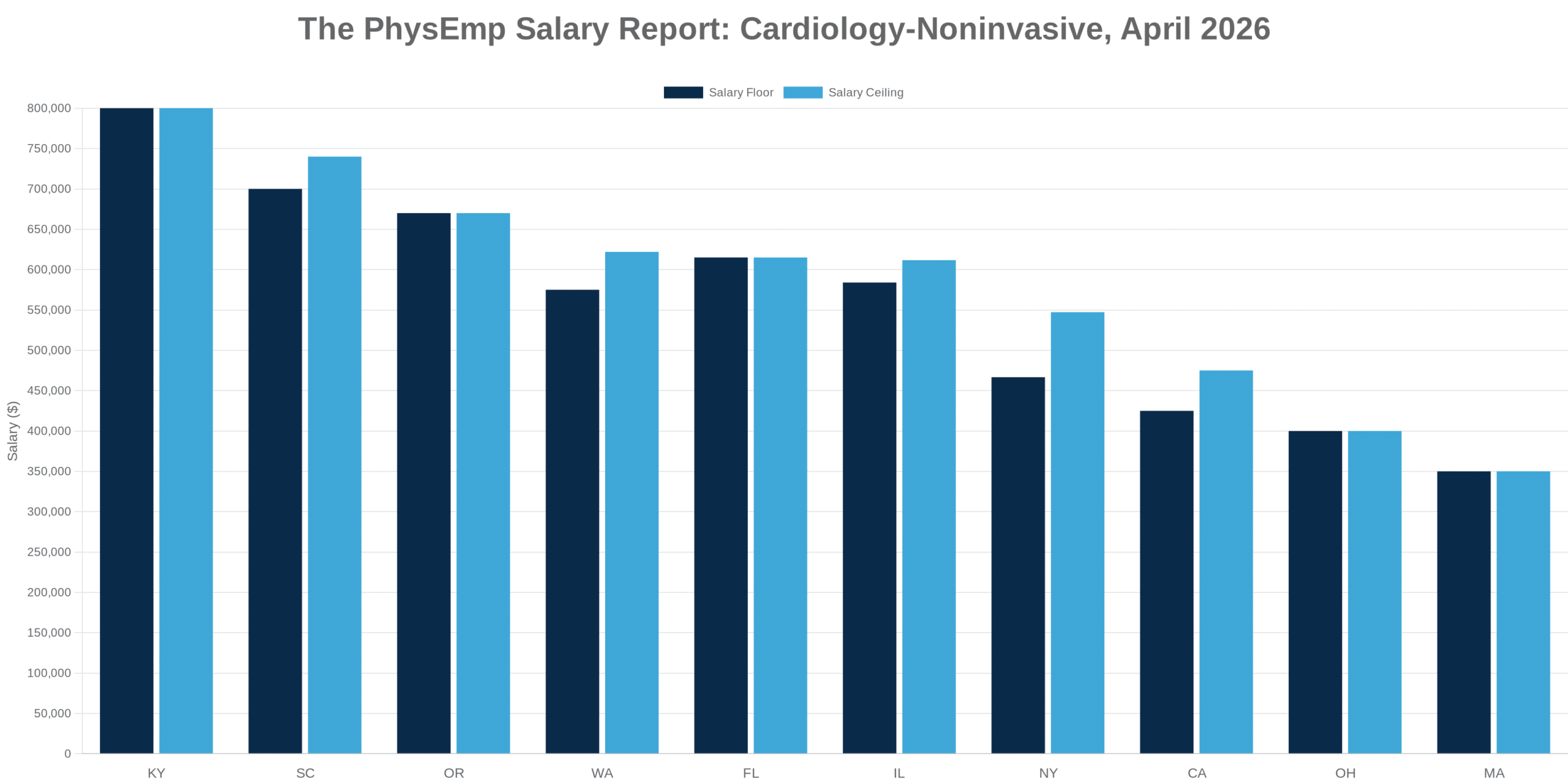
Recruiting the hybrid talent healthcare needs
Cybersecurity hiring for health systems must evolve beyond traditional IT skill lists. The highest-value roles are those capable of translating technical findings into clinical risk terms and embedding security practices into care pathways. These hybrid professionals — clinical engineers with security expertise, security leaders fluent in clinical operations, and communicators experienced in crisis response — reduce response latency and improve decision alignment.
Healthcare employers should leverage specialized hiring platforms to find candidates who combine clinical domain knowledge with cyber risk experience, and build internal upskilling programs that fast-track clinicians into security liaison roles. Prioritizing communication ability and domain familiarity over narrowly technical certifications will pay dividends in incident outcomes and staff retention.
Call Out: Recruit for clinical translation: embedding security practitioners within care teams shortens decision cycles and ensures remediation preserves patient safety rather than just system availability.
Implications for healthcare leaders and recruiters
Executives and hiring teams face three immediate imperatives. First, treat cyber incidents as clinical events by including cyber risk on clinical governance agendas and involving clinical leaders in tabletop simulations. Second, adopt collaborative service models to elevate baseline defenses across a region while preserving local clinical decision authority. Third, redesign recruiting and career pathways to produce the hybrid talent that can bridge technology and care.
Practical starting points: run multidisciplinary tabletop exercises quarterly with communications and clinical leaders; map critical clinical workflows to prioritize segmentation and backup strategies; negotiate regional partnership agreements that specify roles and funding during incidents; and revise job families to create cyber-clinical liaison positions with clear career mobility. These steps convert abstract risk into operational preparedness that protects patients, data, and institutional trust.